There are plenty of tools out there that can perform a security audit for your environment, but none of them are using Google’s security best practices.
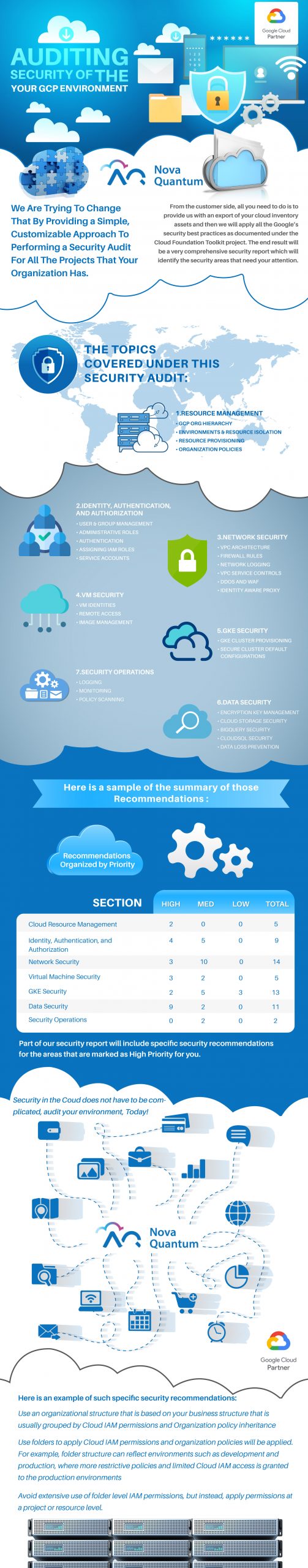
We are trying to change that by providing a simple, customizable approach to performing a security audit for all the projects that your organization has.
From the customer side, all you need to do is to provide us with an export of your cloud inventory assets and then we will apply all the Google’s security best practices as documented under the Cloud Foundation Toolkit project. The end result will be a very comprehensive security report which will identify the security areas that need your attention.
The topics covered under this security audit:
- Resource management
- GCP org hierarchy
- Environments & resource isolation
- Resource provisioning
- Organization policies
- Identity, Authentication, and Authorization
- User & group management
- Administrative roles
- Authentication
- Assigning IAM roles
- Service Accounts
- Network security
- VPC architecture
- Firewall rules
- Network logging
- VPC Service Controls
- DDoS and WAF
- Identity Aware Proxy
- VM security
- VM identities
- Remote access
- Image management
- GKE security
- GKE cluster provisioning
- Secure cluster default configurations
- Data security
- Encryption key management
- Cloud Storage security
- BigQuery security
- CloudSQL security
- Data Loss Prevention
- Security Operations
- Logging
- Monitoring
- Policy scanning
Here is a sample of the summary of those recommendations :
| Recommendations organized by Priority | ||||
| Section | High | Med | Low | Total |
| Cloud Resource Management | 2 | 0 | 0 | 5 |
| Identity, Authentication, and Authorization | 4 | 5 | 0 | 9 |
| Network Security | 3 | 10 | 0 | 14 |
| Virtual Machine Security | 3 | 2 | 0 | 5 |
| GKE Security | 2 | 5 | 3 | 13 |
| Data Security | 9 | 2 | 0 | 11 |
| Security Operations | 0 | 2 | 0 | 2 |
Part of our security report will include specific security recommendations for the areas that are marked as High Priority for you.
Here is an example of such specific security recommendations:
| Use an organizational structure that is based on your business structure that is usually grouped by Cloud IAM permissions and Organization policy inheritance |
| Use folders to apply Cloud IAM permissions and organization policies will be applied. For example, folder structure can reflect environments such as development and production, where more restrictive policies and limited Cloud IAM access is granted to the production environments. Avoid extensive use of folder level IAM permissions, but instead, apply permissions at a project or resource level. |
If you are interested to learn more, signup for your FREE trial of our Google Cloud Platform (GCP) security audit service, today!